An increasing amount of personal data is automatically gathered and stored on servers by administrations, hospitals, insurance companies, etc. Smart appliances surrounding individuals also accumulate spatio-temporal sensitive information (e.g., healthcare monitoring, geo-localization). Citizen themselves often count on internet companies to store their data and make them reliable and available through the internet. However, these benefits must be weighed against privacy risks incurred by centralization. Indeed, there are many examples of privacy violations arising from negligence, abusive use, attacks, and even the most secured servers are not spared.
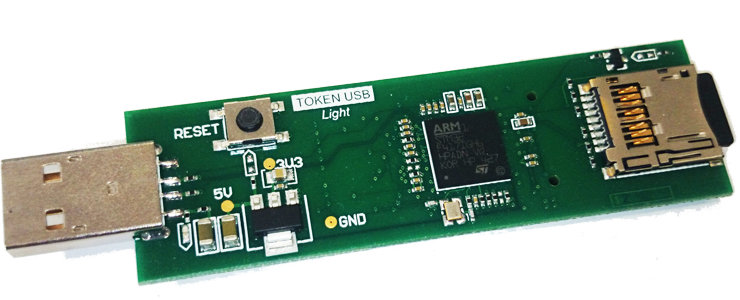
The KISS research initiative draws a radically different vision of the management of personal data. It builds upon the emergence of new portable and secure devices (e.g., mass storage SIM card, secure USB stick, smart sensor) combining the security of smart cards and the storage capacity of NAND Flash chips. The idea promoted in KISS is to embed, in such devices, software components capable of acquiring, storing and managing securely personal data. These software components form a full-fledged Personal Data Server which can remain under holder’s control. However, our approach does not amount to a simple secure repository of personal data. The ambition is threefold. The first objective is to allow the development of new, powerful, user-centric applications thus requiring a well organized, structured and queryable representation of user’s data. Second, we want to provide the data holder with a friendly control over the sharing conditions related to her data and to provide the data recipient with certified information related to their provenance. Third, to give sense to this vision, Personal Data Servers must provide traditional database services like durability, query facilities, transactions and must be able to interoperate with external data sources.
Converting the Personal Data Server vision into reality introduces three main challenges:
- Embedded data management: a Secure Token exhibits strong hardware constraints (e.g., little RAM, NAND Flash storage). Traditional core database techniques need to be fully revisited to design an embedded database engine that provides acceptable performance whatever the form of the embedded data (regular or spatio-temporal).
- Access and usage control: our approach aims at helping individuals to better protect their privacy. The way to control how data is shared and protected must therefore be expressed at high abstraction level. Moreover, proofs of legitimacy must be provided for any data entering or leaving a Personal Data Server whatever the transformation undergone by this data.
- Distributed services: The traditional functions provided by a central server must be re-established in a rather atypical environment combining a large number of highly secure but low power Secure Tokens with a powerful but unsecured server infrastructure.
OBJECTIVES AND EXPECTED OUTCOMES
To tackle these challenges, the KISS consortium relies on the complementary skills of its members and on their past experience to work together: embedded data management (INRIA), access and usage control management (LIRIS), management of widely distributed data and ambient intelligence (UVSQ & LIRIS), cryptography (INRIA & CryptoExperts), smartcard and secure token technology (Gemalto) and finally real use-cases in the context of e-administration (Yvelines District General Council).
The applicability and versatility of the KISS architecture will be demonstrated by the development of two different proofs of concept (e-administration and ambient intelligence). Our objective is that KISS provides an alternative approach to the current systematic centralization of personal data on third-party servers and paves the way for new privacy-by-design solutions dedicated to the management of personal data.
Related publications
-
Toward efficient, privacy-aware media classification on public databases.
Giulia C. Fanti, Matthieu Finiasz, Gerald Friedland, Kannan Ramchandran.
In ICMR 2014, pp. 49, 2014.
-
One-Way Private Media Search on Public Databases: The Role of Signal Processing.
Giulia C. Fanti, Matthieu Finiasz, Kannan Ramchandran.
In IEEE Signal Process. Mag., 2013.
-
Private Stream Search at the same communication cost as a regular search: Role of LDPC codes.
Matthieu Finiasz, Kannan Ramchandran.
In ISIT 2012, pp. 2556-2560, 2012.
-
Private Stream Search at Almost the Same Communication Cost as a Regular Search.
Matthieu Finiasz, Kannan Ramchandran.
In Selected Areas in Cryptography 2012, pp. 372-389, 2012.